Our DNA
Cybersecurity is a corporate mindset
True protection happens at every level, starting with users, through smart training programs and clear communication, and extending through powerful technologies and, most importantly, world-class experts.
We embed security right from the start: integrating change management into projects, implementing clear and precise Identity and Access Management strategies, and setting up rigorous access certification processes.
Framework
RBAC
AI

Access management plays a critical role in safeguarding organizational assets, sensitive data, and intellectual property.
Traditional access control mechanisms, characterized by manual assignment of permissions, are increasingly becoming inadequate in today’s dynamic environments. Logical framework offers a structured approach, aligning access privileges with job roles, responsibilities, and organizational hierarchies.
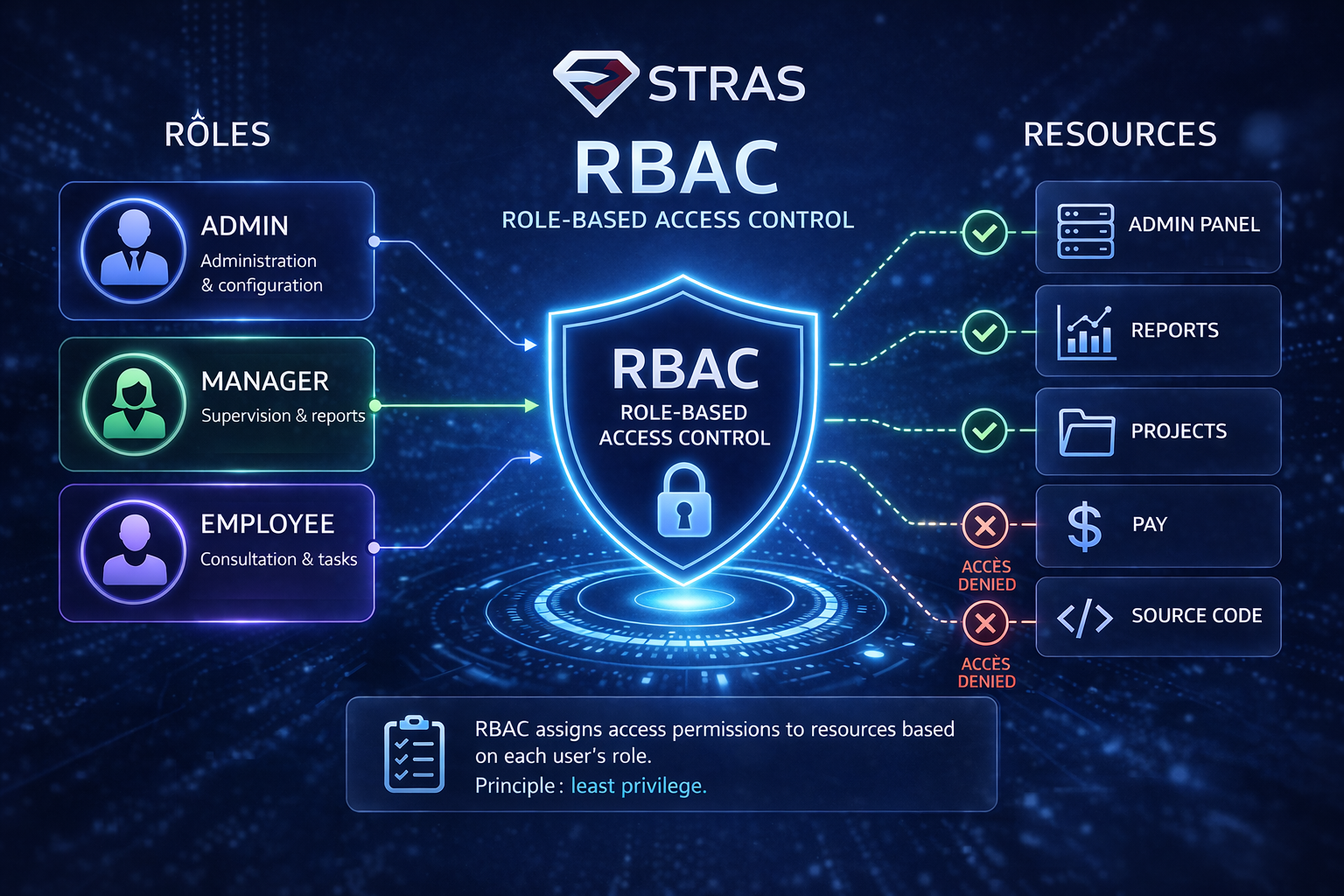
Role-based access control (RBAC) restricts access based on a person’s role within an organization and has become one of the main methods for advanced access control.
An RBAC model allows organizations to manage user access based on clearly defined roles, ensuring that employees only have access to the information and systems necessary for their duties.
By aligning access rights with job functions and automating the employee lifecycle, from onboarding to internal mobility and offboarding, companies can significantly reduce the risk of unauthorized access or data breaches.
Managing access is a complex challenge. We need to understand identities, individual accounts, and technical accounts.
Tomorrow, application accounts will be granted the ability to create their own technical accounts, along with associated access rights. How will you be able to effectively manage the risks that come with this?


IAM Task force – project
OSI





